Configuring site security is an important aspect of ensuring the overall security of your WordPress website. Nginx, as a popular and powerful web server, offers a wide range of security features to protect your website from potential threats. In this article, we will explore how to properly configure Nginx to enhance the security of your WordPress or any other website.
Step-by-step: Configure to Secure a WordPress Site with Nginx
Nginx is a popular, free and open-source web server with high traffic handling capabilities. It is known for its stability, high performance, low resources and simple configuration. However, to ensure security, Nginx’s default configuration needs to be adjusted to prevent attacks and breaches.
Step 1: Install and Configure SSL for WordPress Security
Installing SSL (HTTPS) for your website or Wordpress site will help secure data between users and the server. Websites installed with SSL will increase the level of credibility for visitors. Google also announced that the ranking of websites will improve when using HTTPS.
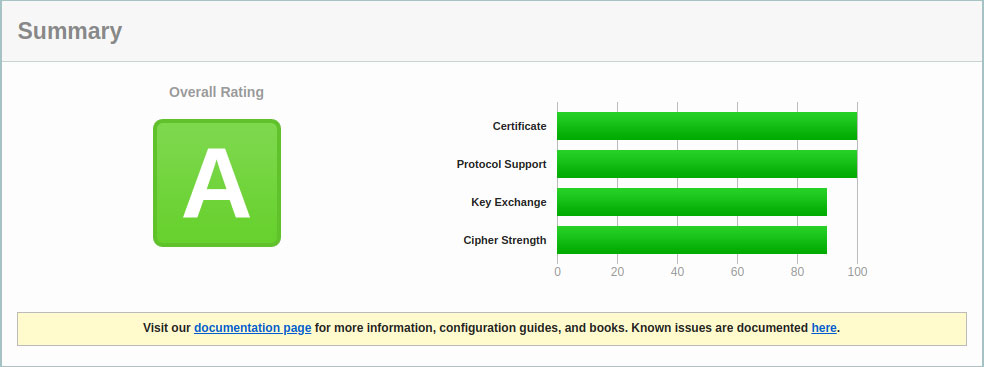
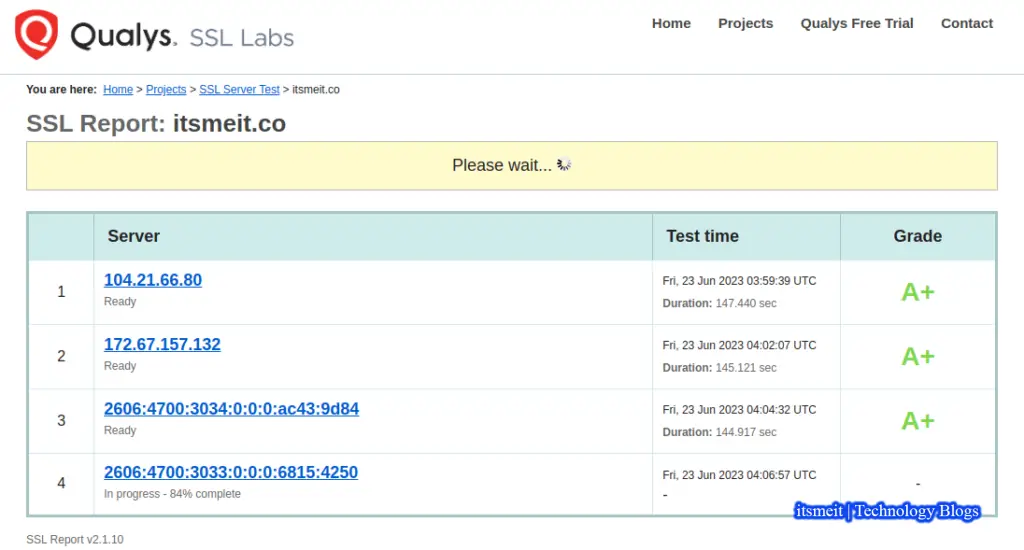
Configure to Secure a WordPress site involves an essential step – installing SSL on an Nginx server. If you’re unfamiliar with the process, you can seek assistance from your hosting provider or VPS server. Alternatively, you can install a free Let’s Encrypt SSL certificate independently. After installation, assess your domain’s security level at SSL Labs.
Step 2: Turn off outdated SSL/TLS protocols
After installing SSL, if your website remains insecure, it’s crucial to configure to secure a WordPress further. TLS versions such as TLS 1.0, TLS 1.1, and SSL 3 are deemed weak and outdated, posing vulnerabilities like POODLE, BEAST, and CRIME, which hackers can exploit, potentially compromising your web server.
In fact, the most popular and widely used web browsers have announced to stop supporting TLS 1.0 and TLS 1.1 like Chrome, Firefox, Safari/Webkit, and Microsoft Edge. To remove outdated SSL/TLS protocols in Nginx, do the following:
Log in to the server and find the file nginx.confin your Nginx configuration. For example ItsmeIT login via SSH and edit the file as follows:
sudo nano /etc/nginx/nginx.conf
Configure to secure a WordPress site with Nginx in SSL/TLS protocol simply remove the old TLSv1 and TLSv1.1 protocols and add TLSv1.2 & TLSv1.3 in the “ssl_protocols” config line.
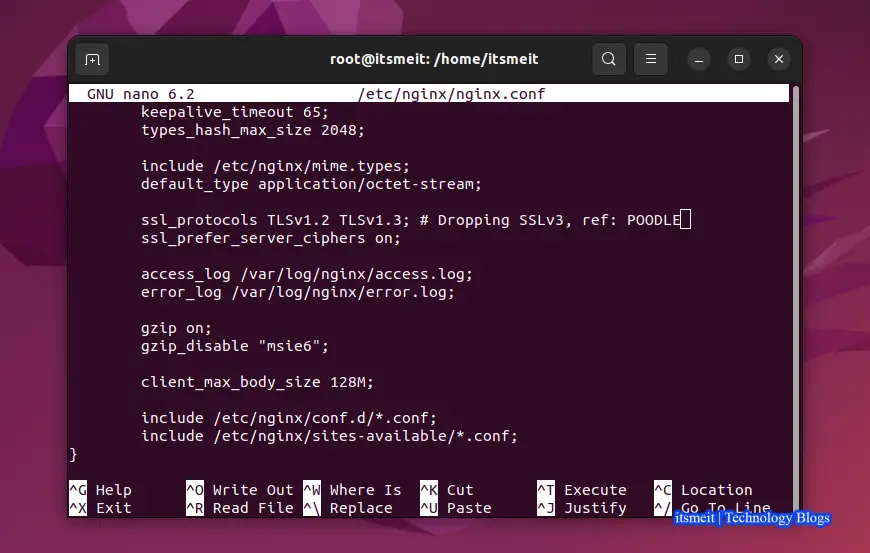
ssl_protocols TLSv1.2 TLSv1.3 ; # Dropping SSLv3, ref: POODLE
Then save the config and restart Nginx.
sudo systemctl restart nginx
Step 3: Prevent server information disclosure Nginx
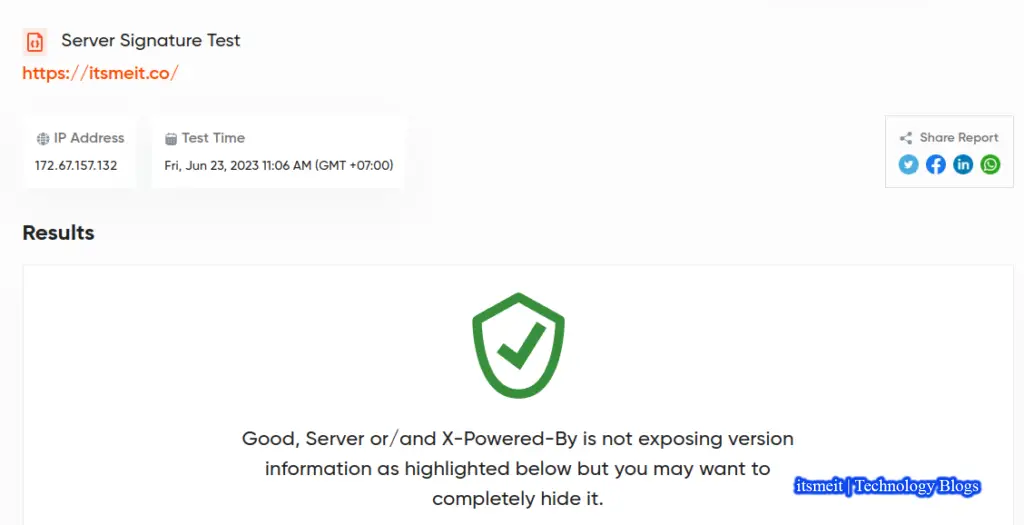
Part of the article on how to secure websites with Nginx (Nginx Server Security) is to turn off the display of nginx server information via HTTP headers. Please try to check the domain name on the website Server Signature Site, if it is a green check mark, your site is secure. If it has a yellow warning X icon, you can do as below and check again.
sudo nano /etc/nginx/nginx.conf
In the http { } configuration you uncomment the server_tokens variable off; is to be. Or if not, add server_tokens off; in http {} is okay. Then restart nginx.
server_tokens off;
Step 4: Block HTTP methods via API
Another way of configuring WordPress site security with Nginx is to disable unwanted HTTP protocols that will not be server implemented by Nginx. The below line will allow implementation of methods GET, POST, HEAD and exclude all other methods including TRACE and DELETE. To do this find your domain configuration file and add the following content.
location / {
# ...
limit_except GET HEAD POST { deny all; }
}Step 5: Prevent Overflow Nginx [Full Memory]
In memory management, a cache is a temporary storage location that holds data as it begins to be moved from one memory location to another.
When the data volume exceeds the capacity of the memory buffer, a buffer overflow occurs. In other words, a buffer overflow occurs when a program writes more data to a block of memory that it can hold or process. So you need to configure nginx to protect your Wordpress site from running out of memory.
An attacker could exploit this vulnerability to send malicious code that could compromise the system. As standard practice, you should make a few tweaks to the Web server to minimize such problems. Continue to open the file nginx.conf and add inside http {} the following content.
sudo nano /etc/nginx/nginx.conf
##buffer policy client_body_buffer_size 1K; client_header_buffer_size 1k; client_max_body_size 1k; large_client_header_buffers 2 1k; ##end buffer policy
Step 6: Prevent XSS . Attacks
XSS (cross-site scripting) is an attack that hackers use scripton a website. When a visitor enters the website, the script is downloaded and can access various browser resources such as cookieand session tokens.
One of the deterrents against such type of attack is to add the line below in the file ssl.confto secure the Wordpress site with Nginx.
add_header X-XSS-Protection "1; mode=block";
Step 7. Preventing Attacks Avoid Clickjacking
To mitigate clickjacking attacks and configure to secure a WordPress site with Nginx, add X-Frame-Options to the HTTP header in the nginx.conf file as shown below, then restart Nginx.

add_header X-Frame-Options "SAMEORIGIN";
Step 8: Block Malicious User Agent
You can block any HTTP user agent with GET/POST requests with your content or attempt to exploit a software vulnerability. To do this continue to open and edit the nginx.conf file adding the following content.
if ($http_user_agent ~* LWP::Simple|BBBike|wget) {
return 403;
}Step 9: Prevent Image hotlinking
Hotlinking is a method where users link images to your website instead of directly uploading the image to their site. When this happens, your images appear on their website and the flip side of this is that you will have to pay extra Nginx server bandwidth.
To do that, open your domain configuration file and add the content below, then restartNginx again. (Replace itsmeit.co with your domain name)
# Stop deep linking or hot linking
location /images/ {
valid_referers none blocked www.itsmeit.co itsmeit.co;
if ($invalid_referer) {
return 403;
}
}You can also specify image extensions as shown to configure WordPress site security with Nginx:
valid_referers blocked itsmeit.co www.itsmeit.co;
if ($invalid_referer) {
rewrite ^/images/uploads.*\.(gif|jpg|jpeg|png)$ https://itsmeit.co/banned.jpg last
}Step 10: Website DDoS Prevention and Mitigation
You can limit the number of connections that a user IP address can open to a limit suitable for actual usage. For example, you can allow each application client’s IP address to open up to 10 connections to your site’s region or store.
limit_conn_zone $binary_remote_addr zone=addr:10m;
server {
# ...
location /store/ {
limit_conn addr 10;
# ...
}
}Above is a summary of some instructions on how to configure website security with your Nginx and secure it from common exploit techniques. This will go a long way in protecting your site files and also the people visiting your Wordpress site.
– Advertising –